Docker seems like it could be ported directly to FreeBSD, but...
Hello, I'm incompetent.
My home server's mysterious sudden death illness still hasn't been resolved, and with ConoHa's VPS going down and even ConoHa's DNS server dying, it was down for a while.
To begin with
It goes without saying that what evolved from jail to become more application-friendly is today's Docker.chroot is merely a change root, an environment where file system level restrictions are imposed. In a sense, you could call it a prison, but it's a bit different. It's just that the root, /, changes.
A convenient and easy-to-understand tool at hand is arch-chroot, but let's try a regular chroot.
thepassenger:[haturatu]:~$ sudo chroot chroot-test/
chroot: failed to run command ‘/usr/bin/bash’: No such file or directoryAs you can see, with the default chroot, bash itself is not visible from within that isolated environment, so you cannot enter it. Furthermore, even if you copy /bin/bash, the dependent libraries that bash requires cannot be referenced from within that isolated environment, so it cannot be executed.
This is Change Root. It's just that the root changes.
sudo mkdir /mnt/arch
sudo pacstrap /mnt/arch base linux linux-firmware man-db vim
sudo arch-chroot /mnt/archJust with the above
thepassenger:[haturatu]:~$ sudo arch-chroot /mnt/arch
==> WARNING: /mnt/arch is not a mountpoint. This may have undesirable side effects.
[thepassenger /]# ls
bin dev home lib64 opt root sbin sys usr
boot etc lib mnt proc run srv tmp var
[thepassenger /]# cd ~
[thepassenger ~]# ls
[thepassenger ~]# ls -la
total 16
drwxr-x--- 4 root root 4096 Mar 31 11:37 .
drwxr-xr-x 16 root root 4096 Mar 31 11:37 ..
drwx------ 3 root root 4096 Mar 31 11:37 .gnupg
drwx------ 2 root root 4096 Mar 31 11:37 .ssh
[thepassenger ~]# If you run ps -ef in this chroot environment afterwards, you'll see that the host machine's processes are still visible from within this chroot.
In the case of FreeBSD's jail, it is further enhanced, separating processes, networks, user space, and so on. Furthermore, Linux's cgroups itself was designed and implemented by Google engineers and has evolved to cgroups v2. My reason for using Docker in the first place is solely for purposes other than easily modifiable resource restrictions, and jail would be fine, but why isn't a similar implementation being done in FreeBSD? This leads to a maze of questions... Can't jail do resource restrictions? No, it can, but why...?
Current state of Docker on FreeBSD
It is still supported, but it's surprisingly old.
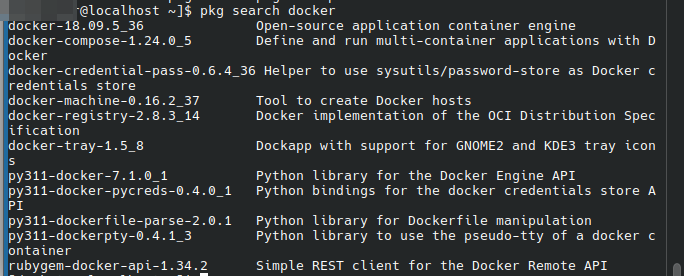
What this means is that while it is supported,
Recent FreeBSD Container Situation #Docker - Qiita
As this article states, it doesn't seem to be maintained anymore.
Furthermore, this FreeBSD version of Docker seems to be merely running Docker via the Linux kernel, rather than being a native implementation.
Can't it be done in FreeBSD?
Frankly, it would be most appreciated if a jail prison environment with full Docker compatibility could be created just by changing an alias.
Resource restrictions can also be achieved by combining it with rctl.
https://codeberg.org/bsdpot/pot
There are also implementations that utilize jail like this, but in a sense, they are implementations within the FreeBSD ecosystem.
In other words, it can be implemented as a container environment. However, the problem with porting is build scripts like Dockerfile. While it's possible to easily convert them into build shell scripts that can be implemented with pot,
FROM
WORKDIR
COPY
ARG
ENV
RUN
EXPOSE It's an unavoidable build language (?) on a layer system like this.
In other words, since their package managers are also different, fully automatic conversion seems a bit difficult. It seems that potfile can handle it, though.
https://github.com/ebarriosjr/potMachine/blob/master/Potfiles/Potfile